Overview
In this tutorial, we will use Chef InSpec to perform testing against our infrastructure.
InSpec can be used to perform local or remote tests and compliance validation for auditing purposes.
Description
The working unit of InSpec is a profile that provides a versioned structure containing checks (i.e. tests); related checks are grouped in "control" blocks. Control is similar to having an high-level rule composed of multiple checks.
In order to check for compliance, the profile along with all respective controls (and corresponding checks) can be run against the local or remote infrastructure; it's also possible to run a single control file.
We'll use the profile dev-sec/linux-baseline that is available in InSpec's supermarket and run it against a remote host.
Please have a look at the control named "os-07".
To run InSpec against a remote host and produce a JUnit XML report that can be submitted to Xray, we may use the following command.
inspec supermarket exec dev-sec/linux-baseline -t ssh://jira:jira@192.168.56.102 --reporter junit:junit.xml
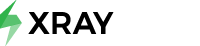
After successfully running the Test Case and generating the JUnit XML report (e.g., junit.xml), it can be imported to Xray (either by the REST API or through Import Execution Results action within the Test Execution).
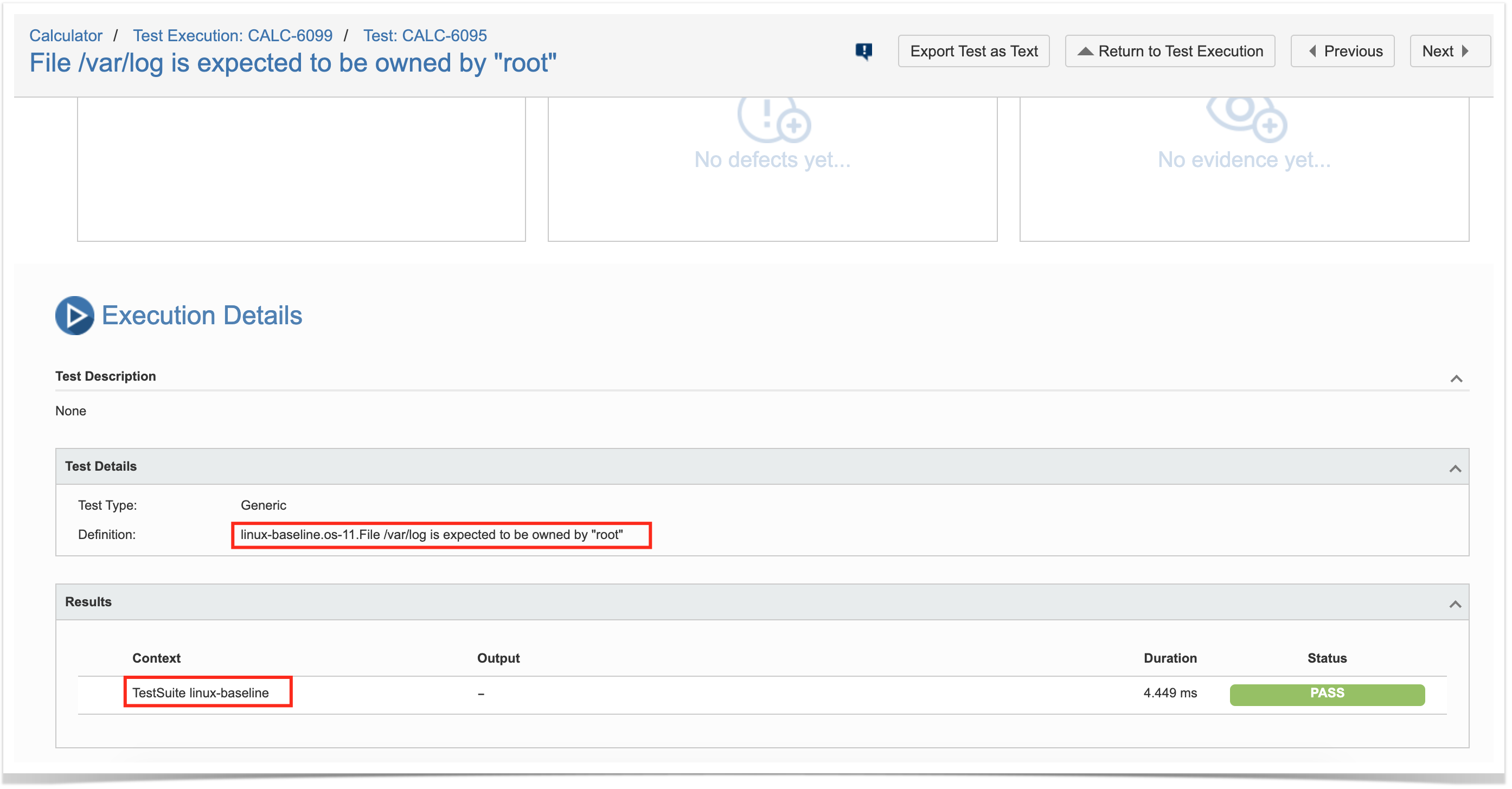
Each check is mapped to a Generic Test in Jira, and the Generic Test Definition field contains the name of the profile followed by the name of the control and the value of the metadata defined using the "desc" attribute within the "control" block.
The Context section contains information about the profile name.
References
- https://www.inspec.io/
- https://www.inspec.io/docs/
- https://learn.chef.io/modules/try-inspec#/
- http://www.anniehedgie.com/inspec/
- https://medium.com/gsktech/always-on-compliance-with-inspec-e3015a229be4
- https://github.com/dev-sec/linux-baseline